PHI data leaks have effected more then 164 million patients between October 2009 and December 2017. (Source: Michigan State University). Also Premera Blue Cross in 2015, was vulnerable to a data leak that leaked the data of 11 million patients. According to the TNS and Chicago Turbine, the Rush University Medical Center was just vulnerable to a 45k patient data leak in May of this year. Internal issues with medical providers as well as EHR vendors, have led to lots of data being sold online, and is noted as one of the most common types of data breaches. This is because we rely on many of the same encryption standards since the 90s. We also have expensive server-wide infrastructure for managing hospital network's IT and security, making it costly, outdated and expensive.
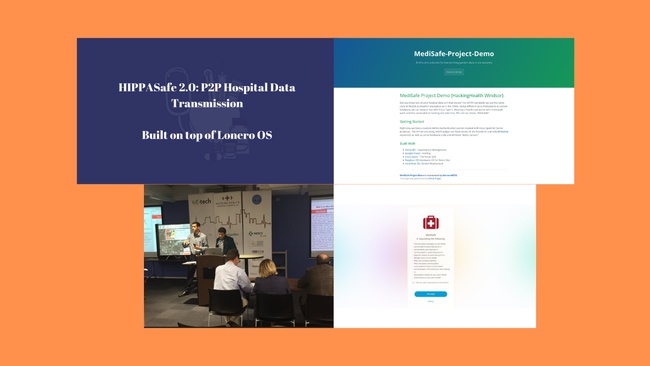
We came up with a solution. A solution that can replace an entire $32k server (which hospital data providers and networks has many of them), replace many IT staff, and fix many of these security flaws. The solution is multi-path layer encryption. I created a hardware cryptography key that makes your computer almost like a middle-ware OAuthenticator, that you connect the key to your computer, it flashes with an OAuth layer, and your localhost now has its own cryptography network with randomized hashing. The hardware key gives hospital personal access to a portal (currently we are trying to phase with Cisco Spark), where they can connect other flashed computers to their network and transmit information between one another.
The solution we have ends up greatly disrupting cyber security. The current key I am working on utilizes a cheap USB with a BIOS and endpoint connectivity. It has 7 pathwall layers, the first being 256 bit, second being 65536 bit hashing compressed, etc., the first layer is extremely difficult to crack (especially given even an implementable randomized hashing algorithm). and the 2nd layer is nearly impossible to hack. Once you reach the 7th hashing layer, most likely the most powerful Quantum Computer in the world couldn't decrypt the key in a decade. What is even more interesting is you can integrate your encrypted network with something like Wireshark and automatically close unauthorized endpoints. In the rare possibility a computer develops some sort of luck-chance in decrypting an earlier path-wall layer they will likely be greeted with the higher challenge or shut down after years of work. Every hospital computer now that is flashed with a hardware key is more secure per computer then the way an entire hospital network is being secured now.
According to John McAfee, and a variety of computer programmers/cyber security experts, we have an outdated grid system and extremely insecure wireless transmission. This plus us being in a literal 5G war with China needs us to come up with more disruptive technology. Lots of the protocols that are being utilized in my hardware cryptography solution, may help come up with a new NIST or Post-Quantum cryptographic algorithmic standard that can lead to a more secure, private, faster, and efficient internet. I believe also with the rise of blockchain, IOT, and unethical hackers trying to steal data, we need solutions like this to push the world forward.